| Resource Type | Purpose |
|---|---|
| **Resource Groups** | Logical containers for all resources (`elestio-{region}`) |
| **Virtual Machines** | Compute instances for your applications |
| **Managed Disks** | OS and data storage for VMs |
| **Virtual Networks** | Network isolation |
| **Network Interfaces** | VM network connectivity |
| **Public IP Addresses** | IPv4 and IPv6 external access |
| **Network Security Groups** | Firewall rules |
| **Storage Accounts** | Backups and object storage |
| **Recovery Services Vaults** | Backup and disaster recovery |
| **Resource Locks** | Prevent accidental deletion |
You can assign the role in the Azure portal by following the steps outlined in the [**Microsoft documentation.**](https://learn.microsoft.com/en-us/azure/role-based-access-control/role-assignments-portal-subscription-admin#step-1-open-the-subscription)
**Verification**: Your account should appear under *Role assignments* with the **Contributor** role. --- #### Step 2: Register Elestio Application in Azure AD [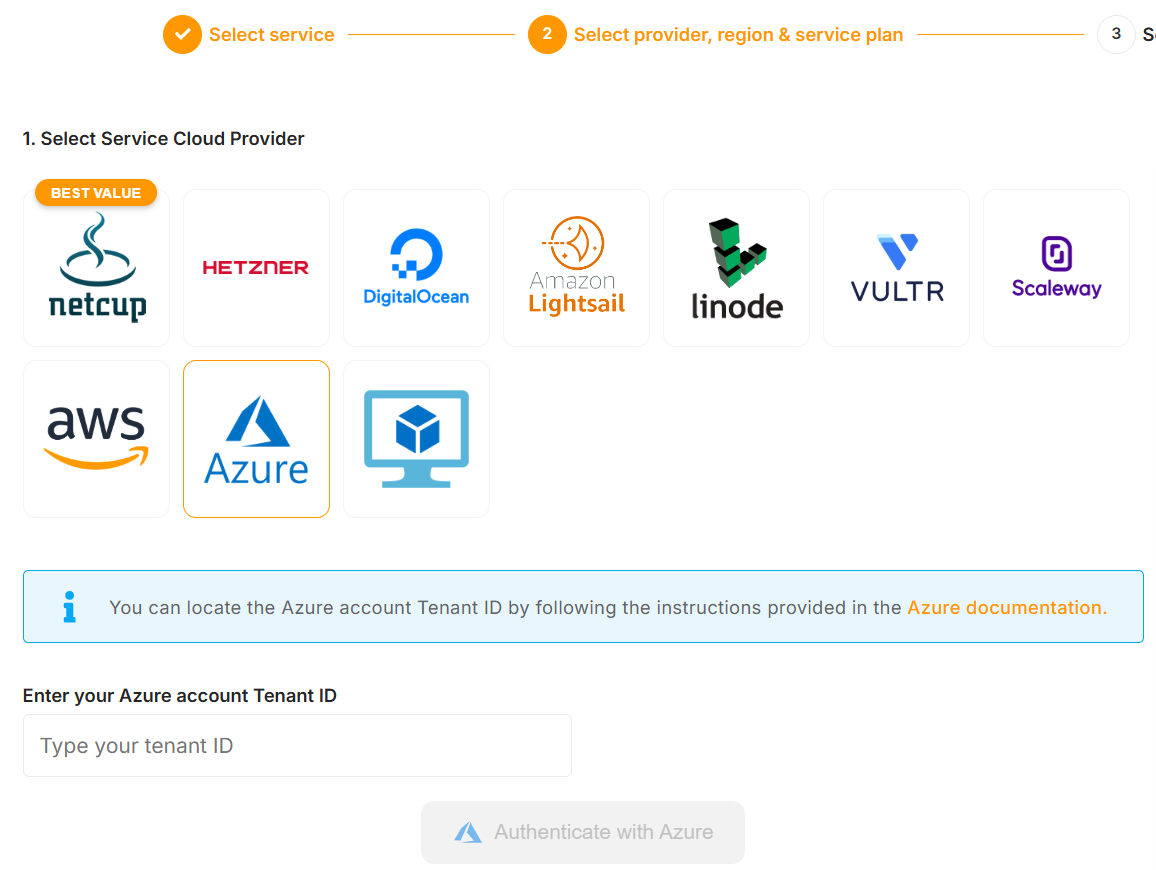](https://docs.elest.io/uploads/images/gallery/2025-12/screenshot-2025-12-24-195252.png) 1. Log in to the Elestio dashboard 2. Select **Software** inside Services. 3. Go to **Cloud Providers → Azure** 4. Enter your **Azure Tenant ID** (see how to find it in the **[Azure portal](https://learn.microsoft.com/en-us/azure/azure-portal/get-subscription-tenant-id#find-your-microsoft-entra-tenant)**) 5. Click **Authenticate with Azure** You will be redirected to the Microsoft login page. --- #### Step 3: Grant Admin Consent [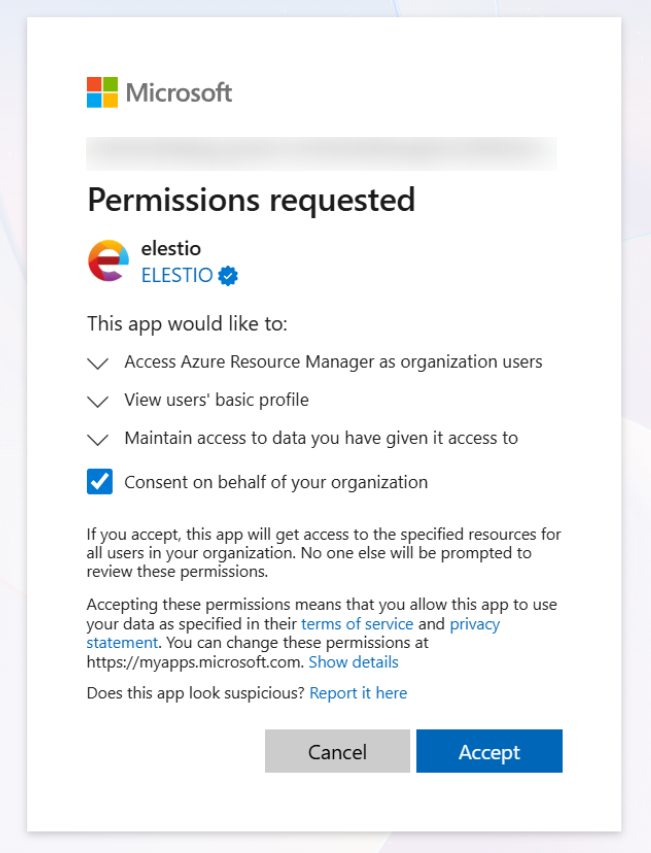](https://docs.elest.io/uploads/images/gallery/2025-12/screenshot-2025-12-24-180102-png-943880-12-24-2025-08-04-pm-1.png) 1. Review requested permissions: - **Access Azure Service Management as you** (`user_impersonation`) 2. Sign in with an admin account if required 3. Click **Accept** > **Note**: If you lack privileges, your Azure AD administrator must grant consent. --- #### Step 4: Select Subscription [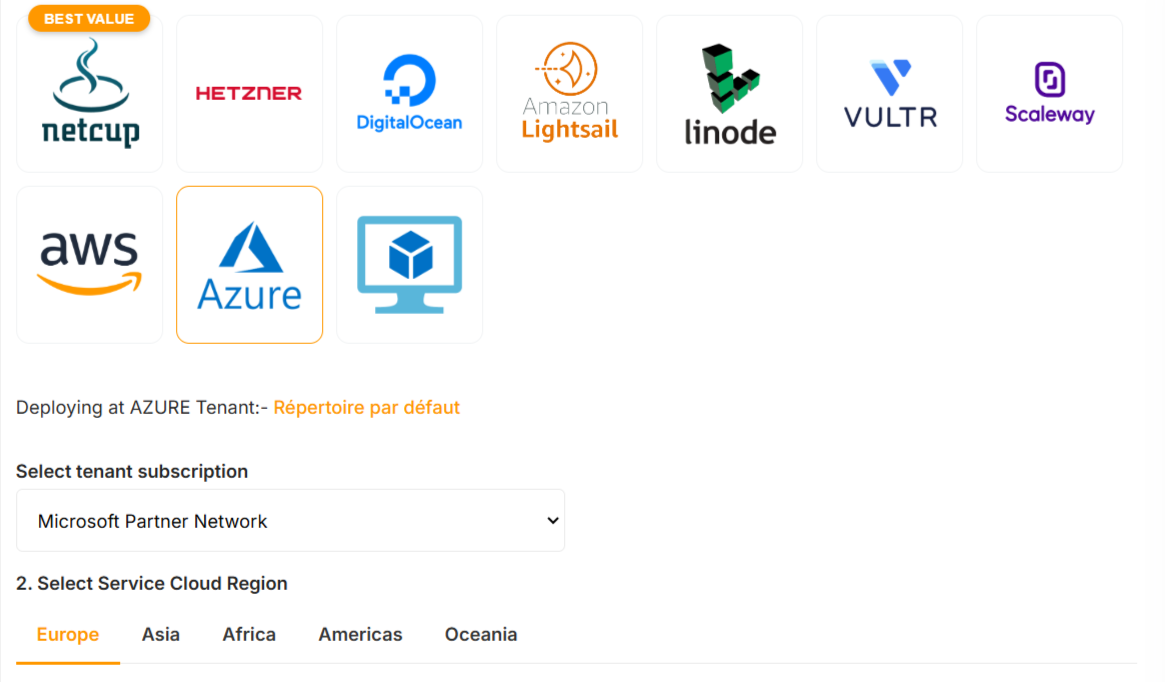](https://docs.elest.io/uploads/images/gallery/2025-12/image.png) 1. Return to the Elestio dashboard 2. Select the Azure subscription. Your Azure account is now connected. --- ### Security Best Practices #### Use Dedicated Subscriptions Recommended for production to ensure: - Clear cost tracking - Workload isolation - Easier audits and compliance --- ### Resource Naming Conventions| Resource | Pattern | Example |
|---|---|---|
| Resource Group | `elestio-{region}` | `elestio-eastus` |
| VM | `{service-name}` | `my-postgres-db` |
| Public IPv4 | `{service-name}_ipv4` | `my-postgres-db_ipv4` |
| Public IPv6 | `{service-name}_ipv6` | `my-postgres-db_ipv6` |
| Virtual Network | `elestio_{region}_vnet` | `elestio_eastus_vnet` |
| Backup Policy | `elestioBackup` | `elestioBackup` |